Security challenges for connected cars
Vulnerability
A common security problem, vulnerability is even more challenging for connected cars with their reliance on third-party hardware and software vendors. Compounding the problem, long product life cycles and supply chains result in products ill-suited to withstand emerging vulnerabilities.
Uncontrollable components
Managing the security risks brought about by the actions of vehicle owners (installing new applications or components, for example) is a difficult task.
Broad scope
Strong connected car security depends on an integrated view of the vehicles, the network, and the back end. And it needs to meet the demands of quickly evolving technology, requiring extensive knowledge and skills.
Lack of threat intelligence
Identifying and preventing cyberattacks against connected cars call for sophisticated threat intelligence, but hosting it requires substantial investment.
Securing the connected car ecosystem
Comprehensive design and visibility are critical.
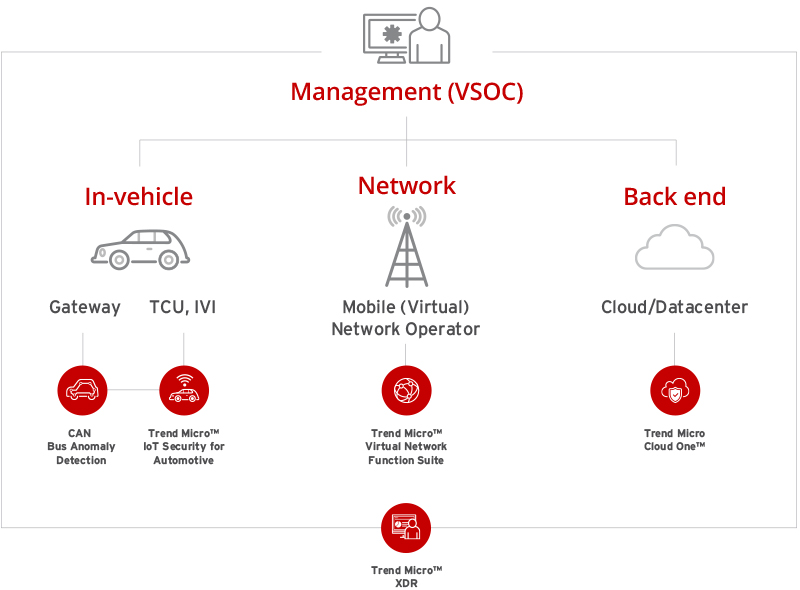
Management of the Vehicle Security Operations Center (VSOC)
It is critical to take a holistic rather than a piecemeal view when considering how to defend against cyberattacks because vehicles, networks, and the back end are so closely linked. This bird’s eye view is indispensable when building a VSOC for monitoring and analyzing events at these points and taking appropriate action against incidents.
In-vehicle
Securing components connected to external and the in-vehicle networks, such as the CAN Bus, is crucial. Once hacked, they can send malicious code to ECUs and nodes. Hacking demonstrations reveal how critical it is to detect and report abnormal behavior. Attackers can exploit vulnerabilities in the TCU/IVI, gaining control over vehicle systems.
Network
Proper network security provision is critical for connected cars. It is necessary to apply security policies that respond flexibly to use cases and requirements, monitor traffic, and detect and prevent threats.
Back end
Demand for back-end connectedness is increasing as multiple applications connected to the cloud for data exchange are sending and receiving information, creating new attack vectors. Successful attacks can have an impact on a larger scale than affecting individual vehicles.
Why Trend Micro
Trend Micro connected car security solutions
For inquiries, email us at info@agdatacom.com
Source: https://www.trendmicro.com/en_ph/business/solutions/iot/connected-car.html
