Public cloud compliance assessment for Amazon Web Services (AWS), Google Cloud Platform (GCP), Kubernetes, and Microsoft Azure ensuring cloud deployments meet various compliance standards (HIPAA, PCI DSS, NIST, GDPR) with the ability to create custom policies for unique governance needs.
![]()
Customized
Policies
Create easy to understand
policies with GSL
![]()
Unified Compliance
Posture
Faster time to compliance across
public cloud environments.
![]()
Reporting and
Auditing
Assessment reports for
security posture status
Automating Compliance
With the proliferation of public cloud applications, compliance teams need to automate IT compliance posture to track status and resolve issues.
Continuous compliance tracking and enforcement is critical. Cloud compliance tools and controls must meet the agile needs of cloud native deployments to ensure compliance and governance of workloads.
Unified Cloud Compliance
The Compliance Engine in the CloudGuard platform delivers end-to-end compliance management with automated data aggregation and in-place remediation for public cloud environments. CloudGuard simplifies the public cloud compliance process and cuts the time to compliance by up to 80%.
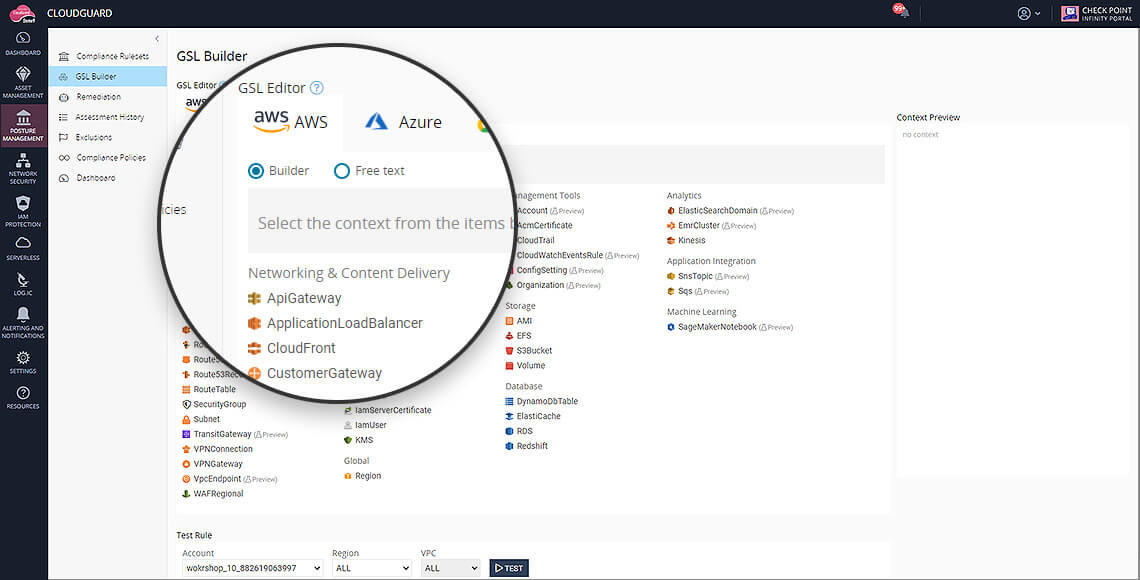
Customized Compliance Policies
Create easy-to-understand policies using the simple yet expressive Governance Specification Language (GSL). A rule that traditionally requires over 100 lines of code can now be written in under 100 characters with GSL. This equates to fewer errors in translating IT governance requirements to policy definitions.
- End-to-end security and cloud compliance management for assessment, remediation and continuous enforcement
- Automated aggregation of data in real-time
- Industry best practices and built-in suites to test compliance against standards such as PCI DSS
- Innovative new Governance Specification Language (GSL) to create custom policies
- Over 500 industry best practices for security encoded
- Printable assessment reports for proof of security posture across business units, virtual networks and cloud accounts
For inquiries, email us at info@agdatacom.com
Source: https://www.checkpoint.com/cloudguard/cloud-network-security/public-cloud-compliance-governance/
